-
AI & ML Cybersecurity: The Latest Battleground for Attackers & Defenders
Machine learning (ML) and artificial intelligence (AI) have emerged as critical tools for dealing with the ever-growing volume and complexity of cybersecurity threats. Machines can recognize patterns to detect malware…
-
SIEM vs. SOAR vs. XDR: What Are The Differences?
Endpoint security and firewalls are two foundational elements of enterprise security, but with remote work, IoT devices and other technologies expanding the boundaries of the network edge, centralized management and…
-
How Hackers Compromise the Software Supply Chain
It seems like a week doesn’t go by without a new vulnerability demonstrating the fragility of the software interdependencies that make up the software supply chain. A large part of…
-
Open Source Sabotage Incident Hits Software Supply Chain
An astonishing incident in recent days highlights the risks of widespread dependence on open source software – while also highlighting the free labor corporations benefit from by using open source…
-
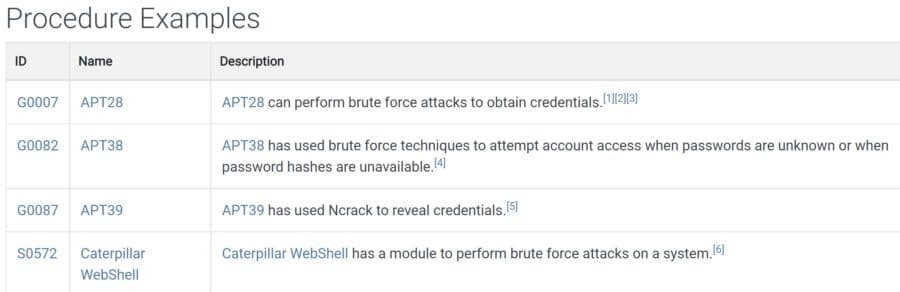
How to Use MITRE ATT&CK to Understand Attacker Behavior
MITRE ATT&CK (“miter attack”) is an up-to-date and widely-used knowledge base that focuses on how attackers think and operate. It’s based on practical use cases, so companies can better evaluate…
-
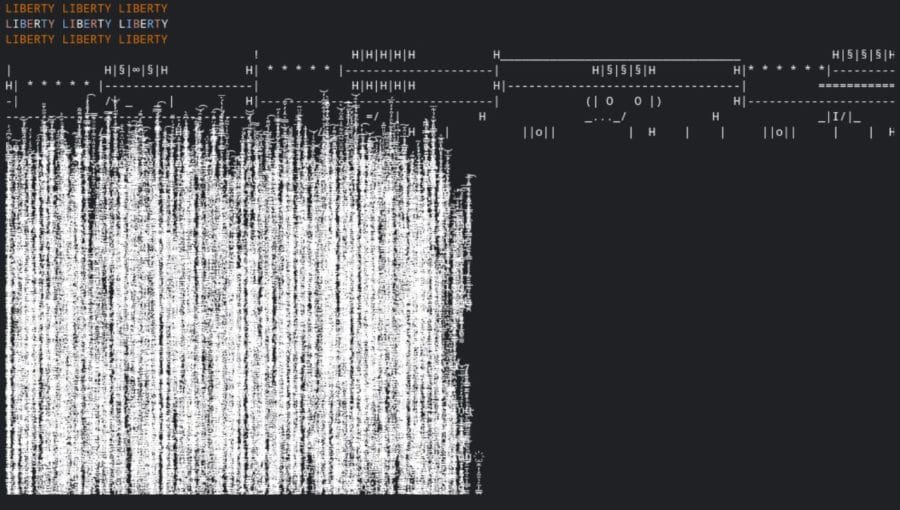
How Hackers Use Payloads to Take Over Your Machine
A payload is a piece of code that executes when hackers exploit a vulnerability. In other words, it’s an exploit module. It’s usually composed of a few commands that will…
-
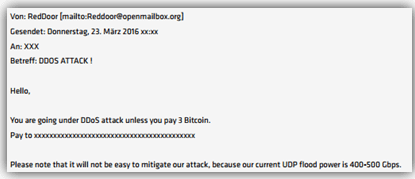
DDoS Attacks Skyrocket, Kaspersky Researchers Say
Distributed denial of service (DDoS) attacks soared in the third quarter, giving organizations yet another cyber threat to worry about. Kaspersky researchers reported that total attacks were up by about…
-
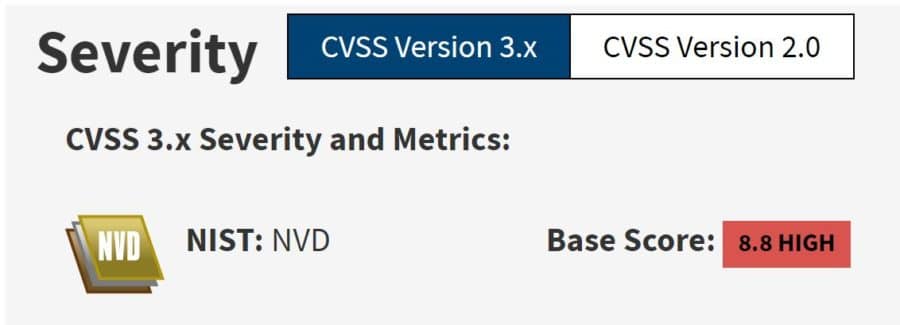
MITRE, CISA Reveal Dangerous Hardware & Software Vulnerabilities
It’s been an active week for security vulnerabilities, with MITRE and the U.S. Cybersecurity & Infrastructure Agency (CISA) revealing hundreds of critical vulnerabilities. CISA ordered federal agencies to patch a…
-
Fake Company Sheds Light on Ransomware Group Tactics
Ransomware groups seem to change form daily. In the latest news, the BlackMatter ransomware group announced it was shutting down – and just hours later came news that its victims…
-
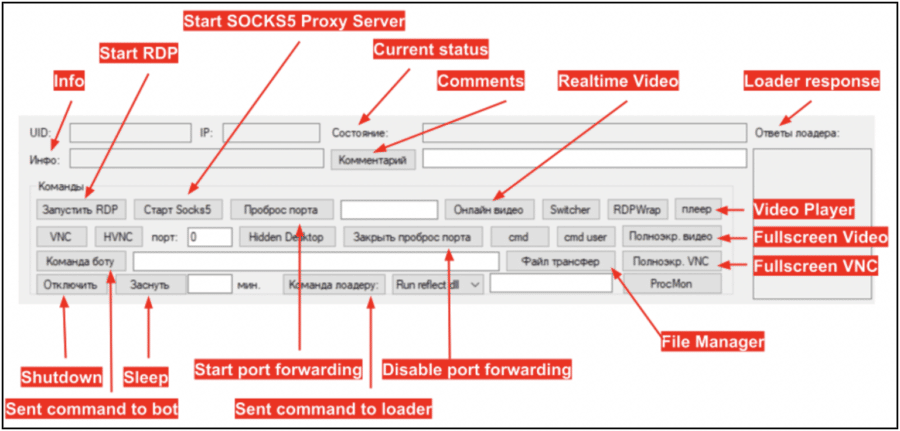
Becoming a Cybercriminal Keeps Getting Easier
Zero-day vulnerabilities are no longer exclusively for elite hackers. There are now automated scripts available on GitHub so even novice hackers can explore these previously unknown security flaws. That was…
Get the free newsletter
Subscribe to Cybersecurity Insider for top news, trends & analysis