Threats
Stay informed on the latest cybersecurity threats and news to better protect your data, networks, applications, and devices. Our coverage includes emerging vulnerabilities, evolving attack techniques, and the latest security breaches to help you understand and mitigate risks.
-
Critical Infrastructure, ICS/SCADA Systems Under Attack by Advanced Threat Groups
Critical infrastructure, industrial control (ICS) and supervisory control and data acquisition (SCADA) systems are under increasing threat of cyber attacks, according to a number of recent warnings from government agencies and private security researchers. CERT-UA (Computer Emergency Response Team of Ukraine) reported a major attack on Ukrainian energy infrastructure last week. Researchers at ESET and…
-
How Hackers Evade Detection
Bypassing detection tools is part of a hacker’s routine these days. Despite the incredible evolution of defensive technologies, attackers often remain undetected for weeks or months, earning the label advanced persistent threat (APT). Classic security tools are necessary but less and less sufficient. That’s why most security companies are now focusing on behavioral analysis and…
-
Protecting Against the Spring4Shell Vulnerability
Spring4Shell (CVE-2022-22965) is a remote code execution (RCE) vulnerability that affects Spring Core, a comprehensive framework for Java-based enterprise applications. Spring4Shell gets its name from the Log4Shell vulnerability, one of the most critical zero-day threats ever, which affected a Java software component called Log4j and allowed hackers to take control of web servers and networks.…
-
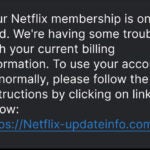
Complete Guide to Phishing Attacks: What Are the Different Types and Defenses?
As web security improves, email security has become a bigger problem than ever. The overwhelming majority of malware attacks now come from email — as high as 89 percent, according to HP Wolf Security research. And with many employees getting multiple emails per day, it’s easy for spam emails to slip their notice and potentially…
-
A Few Clicks from Data Disaster: The State of Enterprise Security
Once an organization has been breached, the overwhelming majority of critical assets are just a few attack techniques away from being compromised, according to a new study. The report by breach and attack simulation (BAS) vendor XM Cyber noted that 63% of critical assets are just a single “hop” away from initial breach to compromise;…
-
Addressing Remote Desktop Attacks and Security
The Remote Desktop Protocol (RDP) has long been essential for IT service management and remote access. Still, in the wrong hands, RDP attacks and vulnerabilities related to remote desktop software are a severe threat. Recent years presented a torrent of research showing how vulnerable RDP systems are for organizations not taking additional cybersecurity precautions. Because…
-
LAPSUS$ Cyber Crime Spree Nabs Microsoft, Okta, NVIDIA, Samsung
The LAPSUS$ threat group has had an attention-grabbing month, snaring high-profile victims like Microsoft, Okta, NVIDIA, Samsung and others. On March 22, Microsoft confirmed a substantial breach by the LAPSUS$ hacking group. In a blog post detailing its efforts to track and contain the breach, Microsoft described LAPSUS$ as a “large scale social engineering and…
-
APT Attacks & Prevention
A company that discovers that an advanced persistent threat (APT) attack is underway tends to be the exception. Attackers design APTs to be subtle, persistent, and to remain undetected for as long as possible. And they tend to succeed at remaining undetected. The average “dwell time” – the period between infiltration and detection – has…
-
Biden Approves Cybersecurity Reporting, Issues Rare Warning
President Joe Biden has faced a number of crises since taking office in January 2021, but his Administration has nonetheless managed to be at the forefront of the U.S. response to cyber attacks by crime groups and hackers aligned with nation-states. Even before Biden took office, the U.S. faced threats like the SolarWinds attack and…